Encryption is the only way one can protect his files and documents from the access of malicious users. I have wrote a number of posts on software can encrypt files and folders and hide it fro curious eyes. Encryption Apparatus is a new portable freeware that can encrypt any file with ease. According to the developer,
This software is designed to secure anything that others shouldn’t know. When encrypting, it creates new file, adds a tag and then writes changed bytes from the original file, regarding to the key. When decrypting, it creates new file named as the original, removes tag and writes changed back bytes from the crypted file. If the key is correct, decrypted and original files will be the same.
Features and Specifications
- The software can be downloaded as a Zip archive [EncryptionApparatus.zip ; 772 Kb] containing the standalone executable along with a read me file.
Download Link
http://themozg.ucoz.com/EncryptionApparatus.zip
- The software is clean of malware and have the following hash.
SHA256: a10edb38db5c1450cd3c57a36a4f12c77e8dd53081ffd031823203ff666e1003
SHA1: 61fdc41def8c880426dc517775e2f9f22bf6a160
MD5: bb53c2e12696dcb2f1b92df0245b2a34
- The application is launched by executing the unsigned standalone executable [EncryptionApparatus.exe ; 1.73 Mb] unzipped from the downloaded archive.
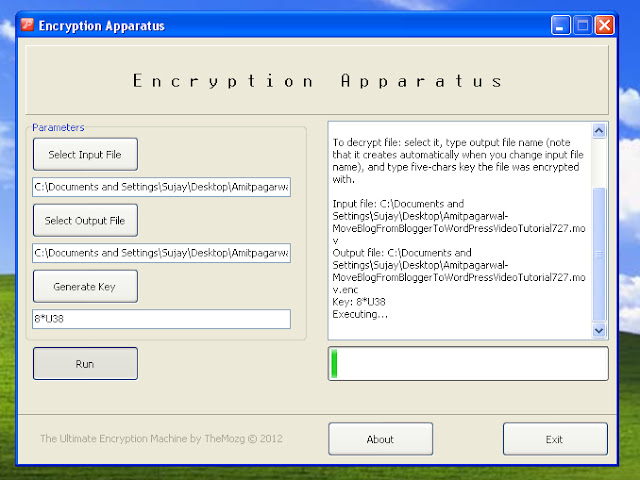
- The software GUI is as simple as it could be.
- The usage is simple, as described in the interface,
To encrypt file: select it, type output file name (note that it creates automatically when you change input file name), and type five-chars key (or generate random one by clicking “Generate key” button).To decrypt file: select it, type output file name (note that it creates automatically when you change input file name), and type five-chars key the file was encrypted with.
- Please remember the key for decrypting purpose.
- The software is portable and can run on any Windows version, both 32 and 64 bit.
- The software uses little system resources at idle time. but moderately high during encryption/decryption.
| System resource Usage at Idle Time |
| System resource Usage during Encryption/Decryption |
My Verdict
This tool has lots of potentials. But at present I am not going to recommend it until it fixes a few issues.
1. It hangs while encrypting a little large files (even with 10 Mb file)
2. It should reduce CPU usage during encryption/decryption.
3. It should not show the key, better hide it behind asterisks. Screenlogger malwares can easily identify that code and will use that for malicious activities.
An useful feature would be to batch process files.
Cheers !!


Hello, Sujay!
First of all, thank you for this review. I really didn't expect anyone to pay attention to my petty works.
Actually, Encryption Apparatus is the first program, that I made in my life and it was created just for fun (and for my school exams too). As you have noticed, it is incapable of doing, what it was designed for. At least, the description on my site is quite fun, eh? =)
I am a little busy now, but I have noted all your suggestions and will update Encryption Apparatus as soon as I have some free time.
Best regards, Fedor.
Windows operating system also provides the feature of encryption, it has a driver named EFS (Encryption File System), and this driver encrypts the files and makes them transparent from attackers who gain access to your system without your permission. The function of EFS is to apply encryption to your files with symmetric key, this symmetric key is also known as File Encryption Key that uses symmetric algorithm.
Windows operating system also provides the feature of encryption, it has a driver named EFS (Encryption File System), and this driver encrypts the files and makes them transparent from attackers who gain access to your system without your permission. The function of EFS is to apply encryption to your files with symmetric key, this symmetric key is also known as File Encryption Key that uses symmetric algorithm. how to encrypt a file